
Authentication Tokens: Why You Should Never Trust the Payload

You know what’s funny? It’s not even July yet, but I’ve already had over twenty conversations that start the same way: “Hey Aşkın, can’t I just grab the user’s email from the access token? The claim is right there!” Happens all the time. My instinct is to launch into a TED talk about why this approach is—let’s call it dicey. But honestly, people need to hear it. Using authentication tokens as if they’re a stable data source? It’s like building a skyscraper on wet cardboard.
Everyone Loves Decoding Tokens… Until They Don’t
This routine pops up everywhere—in DevOps scripts, custom cloud apps, you name it. You get an Azure AD token (or some JWT), base64 decode that sucker (because hey—it looks like neat JSON!), then pull out whatever fields look useful: username, department, tenant IDs, and so forth.
I’m not pointing fingers here; I’ve made this mistake myself. Years ago at Logosoft we did exactly this for an internal dashboard—the team needed group membership info so we decoded tokens and ran with it. Flawless… until one chilly morning in 2020 when Microsoft tweaked their platform and quietly changed some claim names. Access broke for half our users—my phone practically vibrated off my desk.
If your app logic depends on picking apart token claims, you’re tiptoeing along a very thin ledge—and sooner or later gravity wins.
Tokens Are Not Documentation—or Contracts!
Let me be blunt—Microsoft never promised anyone that authentication tokens would have predictable schemas forever (and neither has any other provider worth mentioning). Sure, you can inspect them today—but tomorrow? Or after the next update? There are zero guarantees.
Doğrusu, I run into teams who swear up and down their claims “never change”—it worked for years! Reality check: That just means nobody changed anything upstream yet. Tokens exist to prove identity and permissions—not to act as mini APIs or handy databases squeezed into strings.
Buckle Up—Token Formats Are About To Shift
This isn’t theory anymore; Microsoft plans to ramp up encryption for Azure DevOps tokens this summer (2024) (inanın bana). Could happen sooner depending on which service you’re tied to—a stealth format switch overnight isn’t far-fetched if your luck runs cold.
Dürüst olmak gerekirse, Case in point—I was reviewing an SSO flow last week with a fintech shop in Istanbul when we spotted code extracting crucial user profile details directly from token payloads. We flagged it fast because by September those fields could be scrambled or entirely missing unless fetched through official APIs instead (ben de ilk duyduğumda şaşırmıştım)
The Fallout When Tokens Morph Under Your Feet
Bak şimdi, Picturing disaster helps sometimes—imagine your application expects "department" inside every token because that’s how permissions work today. Overnight Microsoft shifts their identity backend; now “department” either disappears or gets renamed something weird like “dept”. Result? Users locked out… chaos ensues… tickets pile up faster than coffee orders at Monday standup meetings. I’ve watched entire systems go dark because of stuff just like this—not exaggerating!
If Token Claims Aren’t Safe—What’s Next?
You might wonder aloud (and rightfully): “So Aşkın… if I shouldn’t use claims from decoded tokens for business logic where am I supposed to fetch these values?” Good question!
- Treat authentication tokens as opaque: Use them only as proof someone is who they claim—and maybe what they’re allowed to do at that moment.
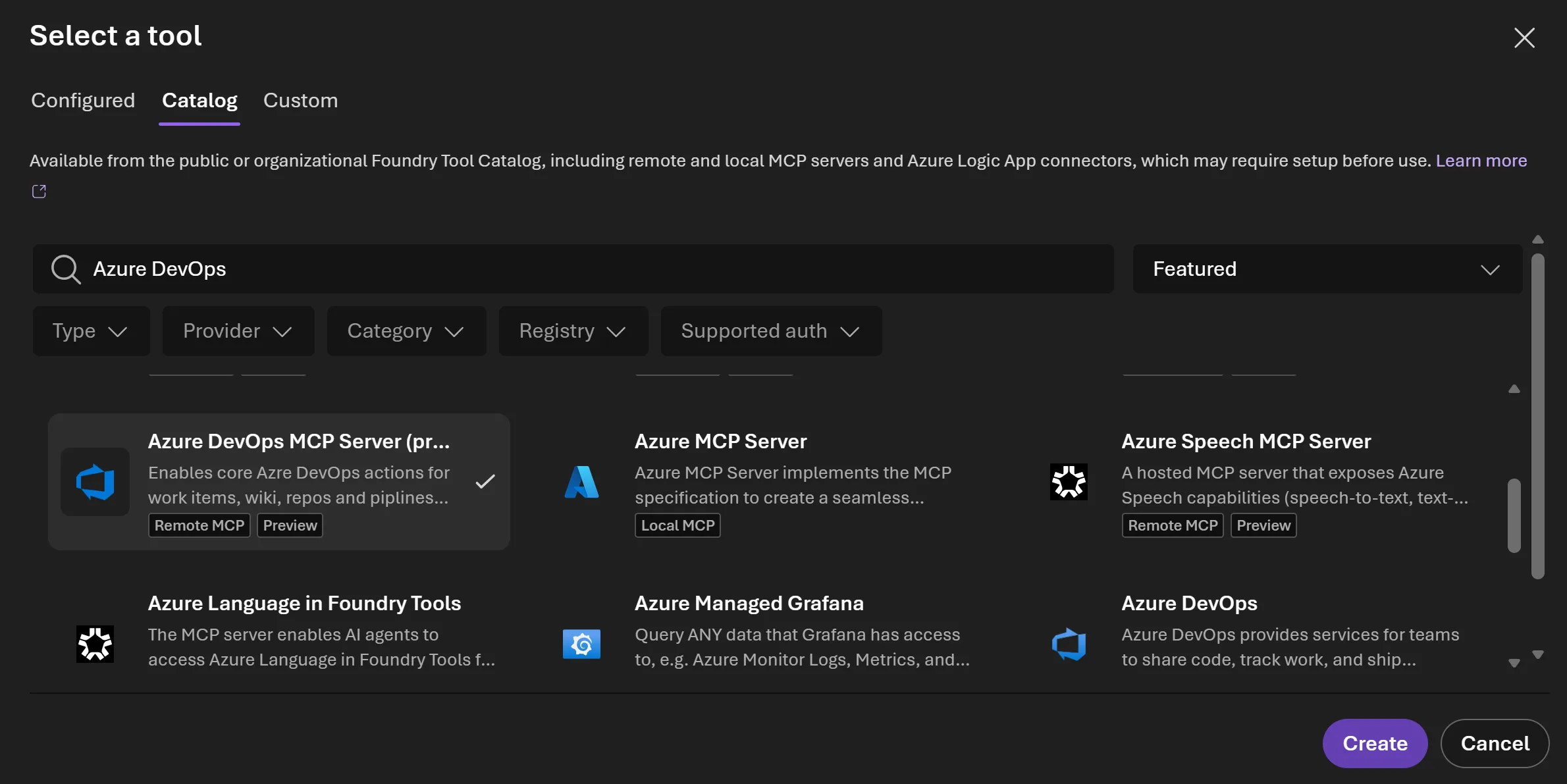
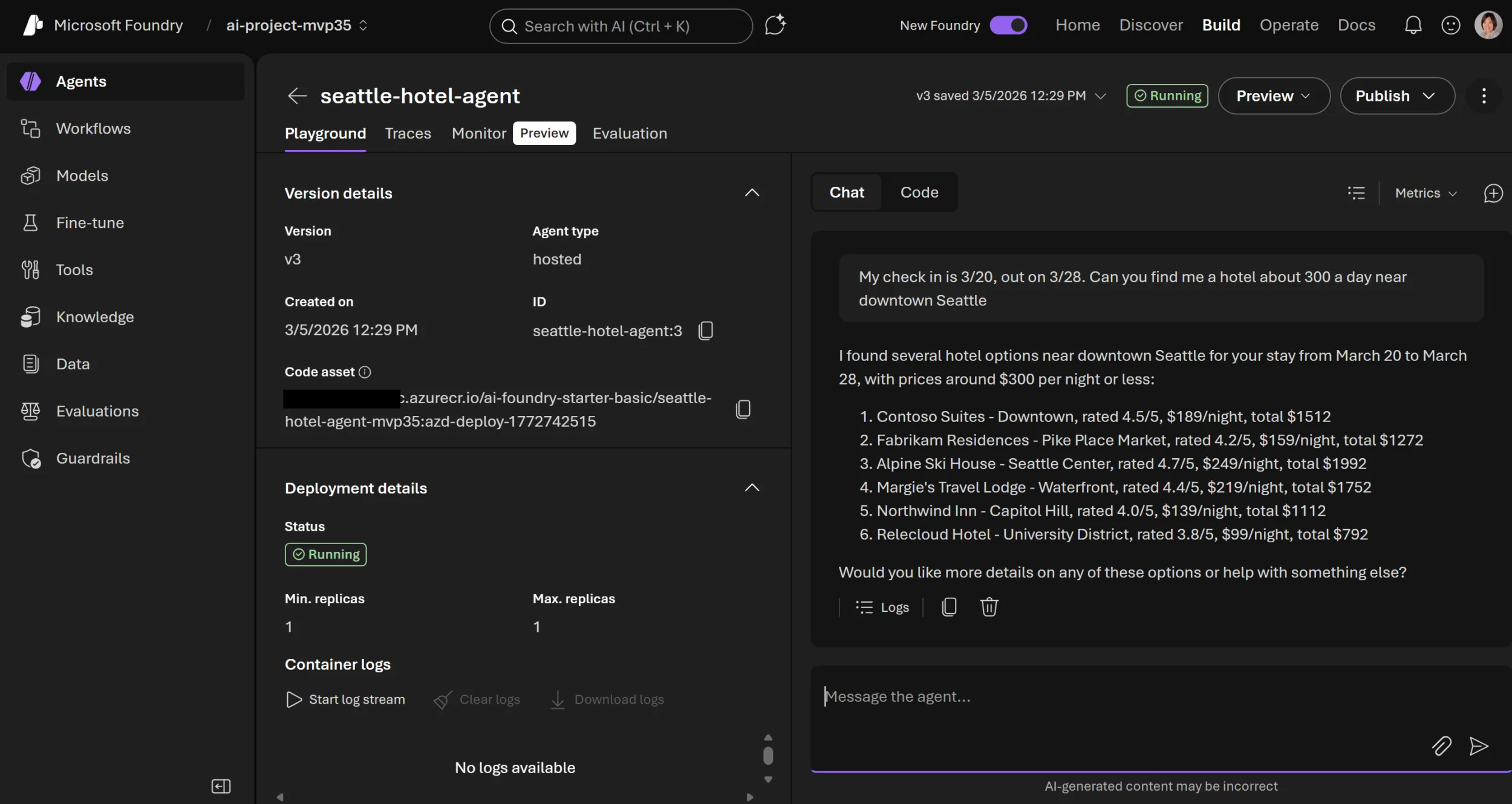
- Fetch real user metadata via supported APIs: Need organization details? Profiles? Grab them using documented REST endpoints—like Azure DevOps or Microsoft Graph—which actually promise stability/versioning.
- Avoid hard-coding dependencies on token structure: Anytime you see yourself digging into
.payload['role'], stop right there! Rethink before production gives you headaches later.
I watched a retail chain migrate legacy apps last December—they ditched direct token inspection after login and switched everything over to Graph API queries instead. Did logins get slightly slower (~half-second hit)? Yes—but security went way up and future breakage risk basically evaporated overnight.
Worth every millisecond lost, hands down. Azure DevOps Remote MCP Server Preview: Real-World Impressions and Tips yazımızda da bu konuya değinmiştik. Azure DevOps Server Patch 2: What You Really Need to Know in 2026 yazımızda da bu konuya değinmiştik.
The Right Approach Looks Like This:
# Pseudocode
# WRONG:
decoded_token = decode(token)
user_department = decoded_token["department"] # BAD
# RIGHT:
user_id = verify_token(token)
user_profile = call_official_api(user_id)
user_department = user_profile["department"]
The Annoying Truth About Opaque Tokens
No denying—it feels quicker/simpler parsing whatever juicy JSON comes back during auth flows than making extra network calls afterwards! Less boilerplate too… But each shortcut here costs double later.
Let me tell you about my ex-colleague from Logosoft—he ignored warnings about opaque tokens while replatforming old apps from another provider until one weekend his entire test suite crashed courtesy of surprise payload changes slipped in via SDK update.
Messy outcome—and totally avoidable had he used proper API calls instead of decoding blobs hoping nothing shifted under him!
“But My Token Format Hasn’t Changed In Years!”
This line pops up nearly every month—I’ve heard folks insist third-party auth providers gave them “guaranteed stability.” Hate to break it but unless official docs spell out contractual support/versioning—you’re flying blind.
Providers routinely encrypt/drop claims as security evolves—even when customers hope otherwise! The only thing set in stone is published API contracts—not how random strings get bundled inside auth tokens day-to-day.
If peeking inside token payloads feels shady—that’s probably because you’re trespassing past intended boundaries!
Your Survival Guide Before Things Break Down
If any chunk of your codebase (or partner product!) currently parses authentication tokens looking for keys beyond bare essentials ('sub', 'exp', etc.), fix ASAP—not next sprint cycle! Waiting invites outages nobody wants…
- Audit everywhere you decode/extract values from tokens: Scan repos/scripts/tools searching for direct usage leaking into app logic.
- Migrate away from risky claim reliance: Refactor so critical details flow through trusted REST endpoints/API calls only—not string decoding games!
- Pilot tests against encrypted/opaque formats early: Mock scenarios where fields disappear/become unreadable—and confirm everything keeps working safely regardless!
- Sensitize everyone writing code around this problem: Get devs onboard fast—a single careless dependency can snowball into tomorrow’s crisis ticket avalanche.
Treat Tokens As Sealed Containers — Future You Will Be Grateful!
I know—it’s tempting treat auth tokens like convenient little configuration files waiting for extraction magic whenever needed.
But really—they aren’t meant as portable key-value stores! These are permission slips signed by platforms granting access within shifting boundaries.
Tomorrow afternoon they might become unreadable/encrypted/missing half their contents…and no blog post will warn you ahead of time.
Bottom line:
Invest upfront integrating with official APIs—even if clunkier—for long-term sanity/security/resilience! Learn from others’ pain before repeat mistakes land on your own doorstep…
Got war stories involving broken flows—or want practical migration strategies?
Ping me anytime—I’ve seen most flavors already…and fixed plenty!
Source: Authentication Tokens Are Not a Data Contract
Related Posts











Post Comment